18/07/2002
In the complex landscape of modern IT infrastructure, Active Directory (AD) stands as the cornerstone of identity and access management. Understanding user login history within AD isn't merely a technical exercise; it's a critical component of robust security, regulatory compliance, and efficient troubleshooting. Knowing who has accessed what, and when, can be the difference between a minor hiccup and a major security breach.
This comprehensive guide will delve into various methods for retrieving Active Directory user login history, exploring both native Windows tools and more advanced solutions. Whether you're investigating suspicious activity, preparing for an audit, or simply aiming to improve your network's security posture, mastering these techniques is absolutely essential.
- Why Tracking Active Directory User Logons is Crucial
- Methods for Retrieving Active Directory User Login History
- Comparative Analysis of Methods
- Frequently Asked Questions (FAQs) on Active Directory User Login Reports
- Can I get User Login Logoff Information via the Active Directory Administrative Center (ADAC)?
- Is it possible to see from where a User login attempt is being made in AD?
- How many Active Directory login/logoff events can be registered in the Event Viewer?
- Why are there so many failed login attempts for a user?
- What is the difference between lastLogon and Event ID 4624?
- Conclusion
Why Tracking Active Directory User Logons is Crucial
The ability to track user login events is indispensable for several key reasons, extending far beyond simple curiosity. It provides the granular insight needed to maintain a secure and compliant IT environment.
- Security Investigations: User login history is often the first port of call when investigating security incidents. Events like repeated failed login attempts (indicating potential brute-force attacks) or successful logins from unusual locations or at odd hours can signal a compromise. It helps in identifying whether an account lockout is due to user error or malicious intent.
- Compliance and Auditing: Many regulatory frameworks (e.g., GDPR, HIPAA, ISO 27001) mandate that organisations maintain detailed audit trails of access to sensitive data and systems. Comprehensive login records demonstrate due diligence and aid in proving compliance during audits.
- Troubleshooting Access Issues: When users report problems accessing resources, reviewing their login history can quickly reveal if they've successfully authenticated to the domain, from which machine, and what type of logon was used. This information streamlines the diagnostic process.
- Resource Management: Tracking logon activity can help identify dormant user accounts that are no longer in use, allowing administrators to disable or remove them, thereby reducing the attack surface. It can also provide insights into resource utilisation patterns.
Methods for Retrieving Active Directory User Login History
Active Directory provides several avenues for gathering login information, ranging from built-in graphical interfaces to powerful scripting capabilities and dedicated third-party software. Each method has its own strengths and limitations.
1. Leveraging Windows Event Viewer
The Windows Event Viewer is the primary native tool for examining security events on your Domain Controllers (DCs). Every successful and failed login attempt is recorded here, provided the appropriate audit policies are enabled.
How to Access and Interpret:
1. Open Event Viewer on a Domain Controller.
2. Navigate to Windows Logs > Security.
3. Here, you'll find a wealth of security-related events. For user login history, you'll primarily be interested in specific Event IDs:
- Event ID 4624: Indicates a successful account logon. This is the most important event for tracking legitimate user access. It provides details such as the user's account name, the computer from which the logon occurred, the logon type (e.g., interactive, network, remote interactive), and a unique Logon ID for the session.
- Event ID 4625: Signals a failed account logon. These events are crucial for identifying potential brute-force attacks or misconfigured user accounts.
- Event ID 4634: Represents an account logoff. This event can be paired with a corresponding 4624 event using the Logon ID to determine the duration of a user's session.
- Event ID 4647: Indicates a user-initiated logoff.
- Event ID 4648: Denotes a user logon with explicit credentials, often seen when a user runs a program as a different user.
Prerequisites and Limitations:
For logon events to be recorded, proper audit policies must be enabled via Group Policy Objects (GPOs) and applied to your Domain Controllers. Specifically, you need to enable 'Audit logon events' under 'Computer Configuration > Policies > Windows Settings > Security Settings > Advanced Audit Policy Configuration > Audit Policies > Logon/Logoff'.
While powerful for detailed investigation of individual events, the Event Viewer has significant limitations for comprehensive auditing:
- Manual and Time-Consuming: Sifting through thousands of events across multiple Domain Controllers is incredibly inefficient for large environments.
- Distributed Data: Login events are stored on the specific DC that authenticated the user. To get a complete picture, you must check all DCs.
- Retention Policies: Event logs have a finite size and will overwrite older events unless configured otherwise, leading to data loss over time.
2. Employing PowerShell Scripts
PowerShell offers a more automated and flexible approach to gathering Active Directory login history. It allows administrators to programmatically query event logs and compile reports.
How PowerShell Helps:
The primary command for retrieving event logs is Get-WinEvent (or older Get-EventLog). A well-crafted PowerShell script can:
- Filter events by specific Event IDs (e.g., 4624, 4634).
- Target events within a specific time range (e.g., last 24 hours, last 7 days).
- Extract relevant properties like username, computer name, logon type, and timestamps.
- Match login events (4624) with logoff events (4634) using the unique Logon ID to calculate session durations.
- Generate custom reports, often exported to CSV for further analysis.
For example, a script could iterate through all Domain Controllers, collect relevant security events, and then process them to build a report detailing who logged in, from where, and for how long. Another common use is to get the last logon time for users using Get-ADUser -Property lastLogon. However, it's important to note that the lastLogon attribute is not replicated instantly across all DCs, so it may not always show the absolute latest logon time, and it certainly doesn't provide a history.
Pros and Cons of PowerShell:
Pros:
- Automation: Scripts can automate repetitive tasks, saving significant time.
- Customisation: Highly flexible, allowing for tailored reports based on specific requirements.
- No Additional Cost: PowerShell is a built-in Windows component.
Cons:
- Scripting Knowledge Required: Developing and maintaining complex scripts requires expertise.
- Performance Issues: Processing large volumes of event logs, especially across multiple DCs, can be very slow and resource-intensive.
- Data Aggregation: Still requires careful handling to aggregate data from all DCs for a complete picture.
- Scalability: Can become unmanageable in very large environments with vast numbers of events.
3. Utilising Command Line Tools
While less comprehensive for historical data, certain command-line tools can provide quick snapshots of user activity.
query user /SERVER:servername: This command can show you which users are currently logged onto a specific server. It's useful for immediate, real-time checks but provides no historical data. You need to replace "servername" with the actual server's name.net user <username> /domain: This command provides basic information about a user account, including the 'Last logon' time. Similar to thelastLogonattribute in ADUC, this only shows the most recent logon and isn't a detailed history. It's also domain-level, so it looks across your AD.
These methods are extremely basic and offer minimal utility for comprehensive auditing or historical analysis. They are best suited for quick, ad-hoc checks on a single machine or user.
4. Investigating with Active Directory Users and Computers (ADUC)
Active Directory Users and Computers (ADUC) is the primary graphical tool for managing AD objects. While it offers some limited insight into user logon status, it's far from a comprehensive auditing solution.
How to Access (and its limitations):
1. Open ADUC snap-in.
2. Click on View and enable Advanced Features. This step is crucial as it exposes additional attributes.
3. Find the target user account in an Organisational Unit (OU).
4. Right-click the user and select Properties.
5. Navigate to the Attribute Editor tab.
6. Scroll down or type 'log' to filter attributes. You'll find attributes like lastLogon and lastLogoff.
The significant drawback here is that these attributes only show the last logon/logoff time, not a history. Furthermore, the values are often displayed in a large integer format (FileTime format), which is not human-readable without conversion. This method is strictly view-only and is entirely impractical for tracking multiple users or obtaining historical data for auditing purposes. For any meaningful reporting, you'd need to extract and convert these values, a task better suited for PowerShell.
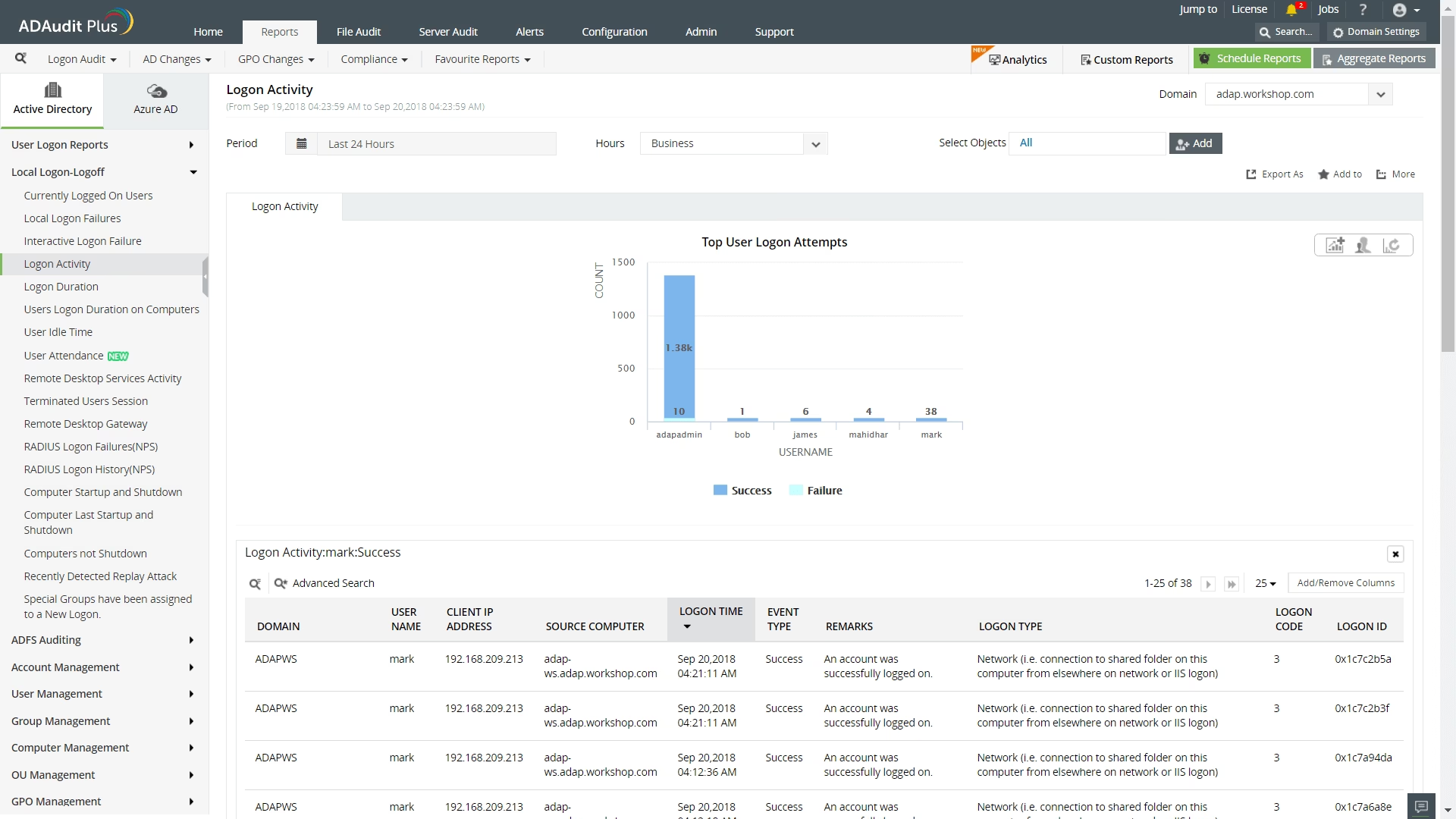
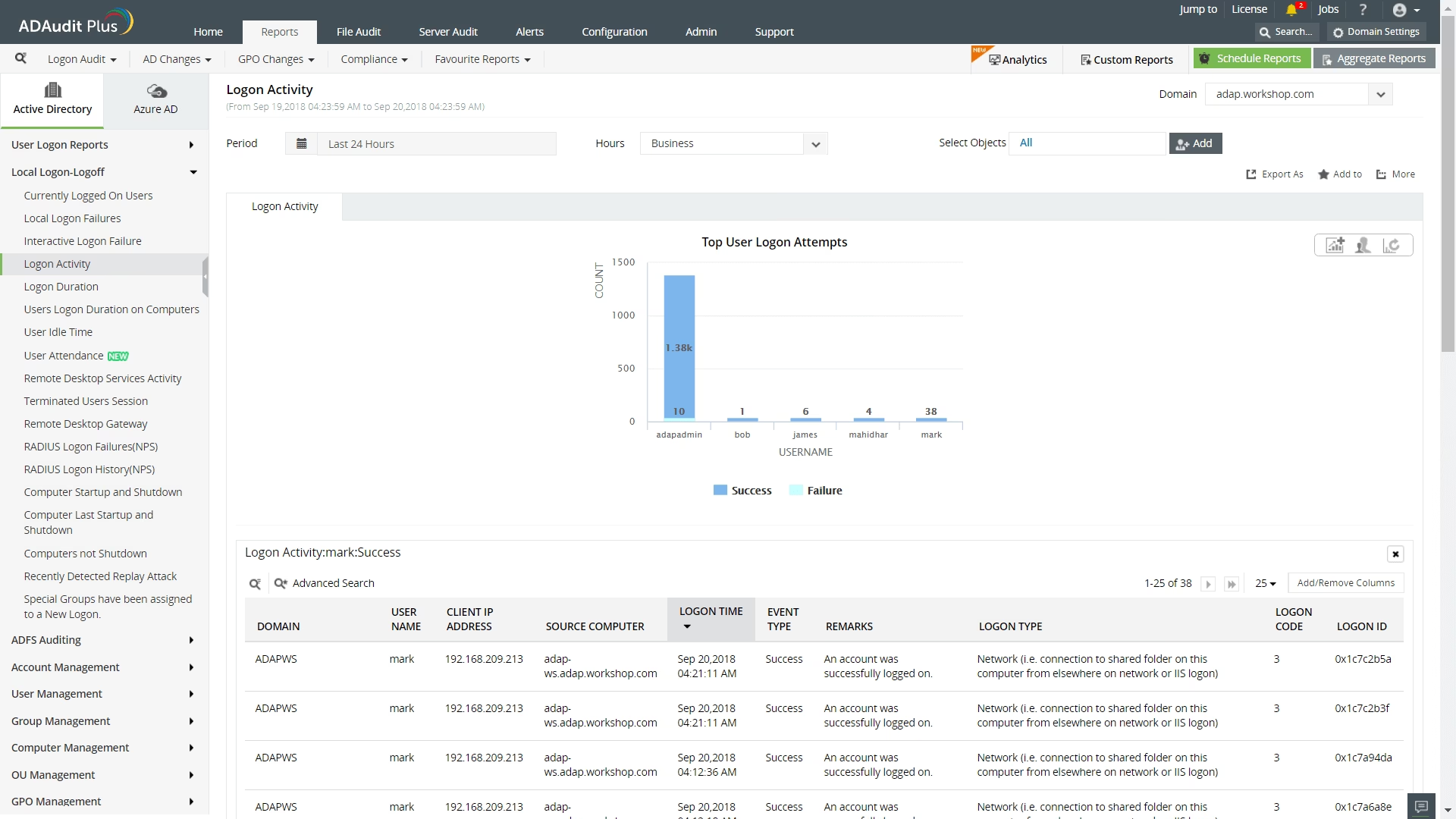
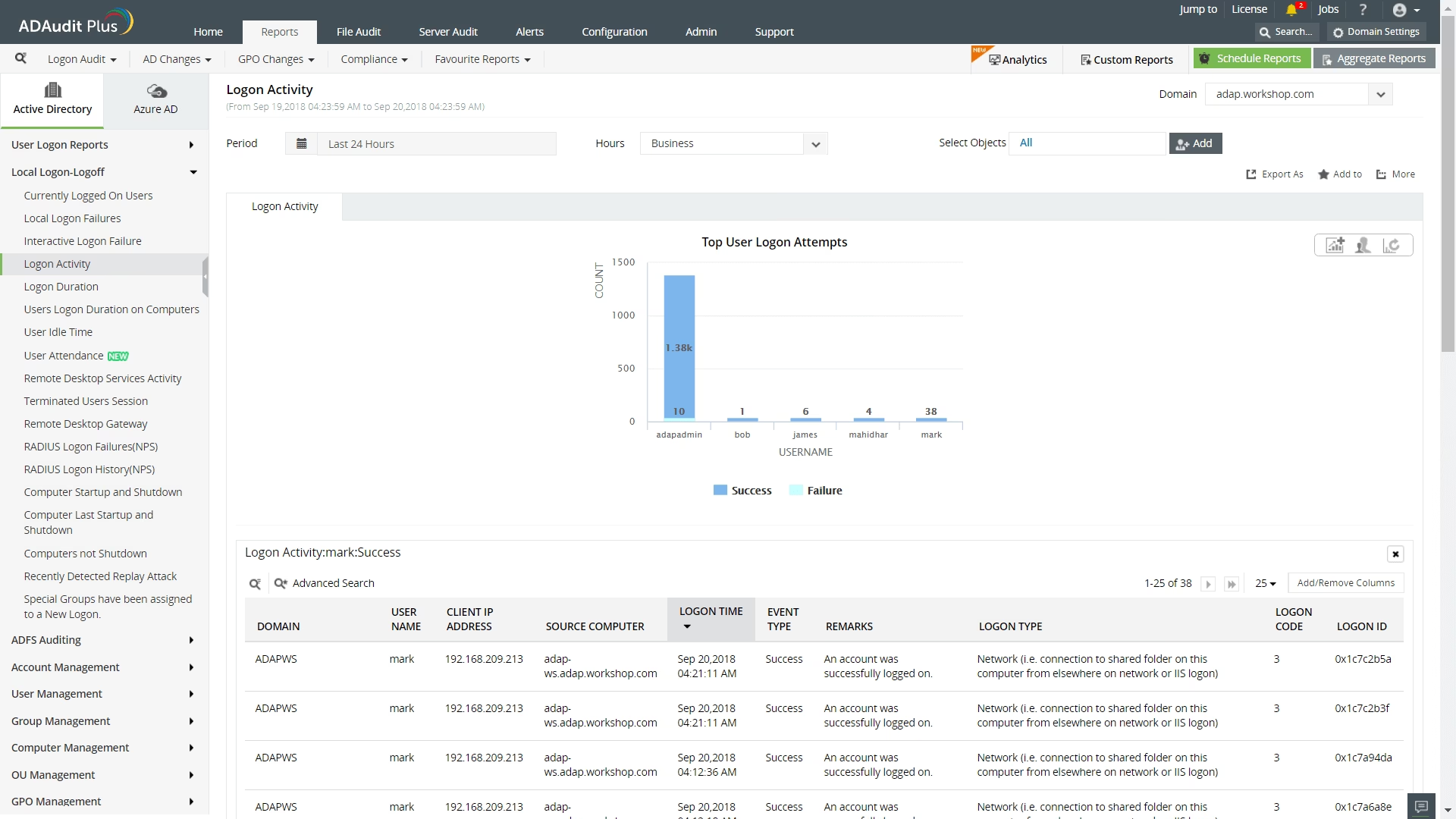
5. The Advantage of Dedicated AD Auditing Software
Given the complexities and limitations of native tools, many organisations opt for dedicated Active Directory auditing software. These solutions are designed to overcome the challenges of manual event log analysis and provide a streamlined, comprehensive view of user activity.
Key Features and Benefits:
- Centralised Data Collection: Automatically collects and aggregates login events from all Domain Controllers, presenting them in a single, unified interface.
- Automated Reporting: Generates detailed, easy-to-read reports on user logins, logoffs, failed attempts, and session durations. These reports can often be scheduled and delivered automatically (e.g., via email).
- Real-Time Alerts: Configurable alerts for suspicious activities, such as logins outside business hours, from unusual IP addresses, or repeated failed login attempts.
- Long-Term Data Retention: Stores audit data for extended periods, fulfilling compliance requirements and enabling historical analysis without relying on limited event log capacity.
- User Behaviour Analytics: Some advanced solutions can analyse patterns to detect anomalies that might indicate a compromised account or insider threat.
- Simplified Compliance: Often include pre-configured reports and dashboards tailored to various compliance standards.
While these solutions typically involve a cost, the time saved, enhanced security posture, and ease of compliance often justify the investment, especially for larger or highly regulated organisations. They transform a tedious, manual process into an automated, insightful operation.
Comparative Analysis of Methods
To help you choose the best approach for your needs, here's a comparative overview:
| Method | Pros | Cons | Best Use Case |
|---|---|---|---|
| Windows Event Viewer | Granular details, built-in, free | Manual, distributed data, time-consuming, limited retention | Deep dive into a specific, isolated incident on one DC |
| PowerShell Scripts | Automated, highly customisable, free | Requires scripting expertise, slow for large datasets, complex aggregation | Ad-hoc reports for specific requirements (if skilled), basic automation |
| Command Line Tools | Quick check for current sessions, simple | Very limited, no historical data, basic 'last logon' only | Immediate, superficial checks on a single server/user |
| ADUC | Built-in, no special tools needed | Extremely limited (last logon only), unreadable format, no history | Basic visual check of a single user's last login time (not recommended for reporting) |
| Dedicated Auditing Software | Comprehensive, automated, easy-to-read reports, real-time alerts, long retention | Cost involved, initial setup/learning curve | Continuous monitoring, compliance, large/complex environments, proactive security |
Frequently Asked Questions (FAQs) on Active Directory User Login Reports
Here are some common questions regarding Active Directory user login history:
Can I get User Login Logoff Information via the Active Directory Administrative Center (ADAC)?
Similar to ADUC, the Active Directory Administrative Center (ADAC) primarily focuses on managing AD objects. While you can view properties of users, it does not provide a historical log of login/logoff events in a reportable format. For detailed history, you must rely on event logs or dedicated tools.
Is it possible to see from where a User login attempt is being made in AD?
Yes, Event ID 4624 (successful logon) includes the 'Source Workstation' or 'Source Network Address' (IP address) from which the logon attempt originated. This information helps identify the specific computer or network location involved. However, Active Directory itself does not provide geographical location data; for that, you'd typically need to integrate with IP-to-geolocation services or use advanced security information and event management (SIEM) solutions.
How many Active Directory login/logoff events can be registered in the Event Viewer?
The number of events depends entirely on the configured maximum size of the Security Event Log and its retention policy (e.g., 'Overwrite events as needed', 'Archive the log when full', or 'Do not overwrite events'). Once the log reaches its maximum size, older events will be overwritten unless archiving is enabled. This is why long-term data retention for auditing often necessitates offloading logs to a central log management system or using dedicated auditing software.
Why are there so many failed login attempts for a user?
An unusually high number of failed login attempts for a specific user can indicate several issues:
- Typographical Errors: The user repeatedly enters the wrong password.
- Cached Credentials: A common scenario involves mobile devices or applications holding outdated credentials after a password change, causing continuous attempts to authenticate with the old password.
- Brute-Force Attack: A malicious actor is attempting to guess the user's password.
- Misconfigured Service Accounts: Services or scheduled tasks configured with incorrect passwords will repeatedly fail authentication.
Investigating these failures promptly is crucial to prevent account lockouts and identify potential security threats.
What is the difference between lastLogon and Event ID 4624?
The lastLogon attribute on a user object in Active Directory is a property that indicates the time of the *last successful* user logon. This attribute is not replicated instantly across all Domain Controllers; it typically replicates every 9-14 days. Therefore, it's not reliable for real-time or precise last logon information. Event ID 4624, on the other hand, is an event generated in the Security Event Log of the specific Domain Controller that authenticated the user. It is real-time, granular, and provides much more detail about the logon event, including the logon type and source IP. For accurate and detailed login history, Event ID 4624 (and related logoff events) is the authoritative source.
Conclusion
Understanding and effectively managing Active Directory user login history is a fundamental aspect of maintaining a secure and compliant IT environment. While native Windows tools like the Event Viewer, PowerShell, command-line utilities, and ADUC offer varying degrees of insight, they often come with significant limitations, especially in terms of scalability, automation, and ease of reporting.
For organisations seeking comprehensive, automated, and streamlined auditing capabilities, dedicated Active Directory auditing software provides a robust solution. These platforms overcome the inherent challenges of native methods by centralising data, offering intuitive reports, providing real-time alerts, and ensuring long-term data retention. Ultimately, whether through painstaking manual effort or powerful automated systems, the ability to track and analyse user login patterns remains paramount for protecting your Active Directory and the critical resources it safeguards.
If you want to read more articles similar to Mastering Active Directory Login History, you can visit the Automotive category.
