05/07/2019
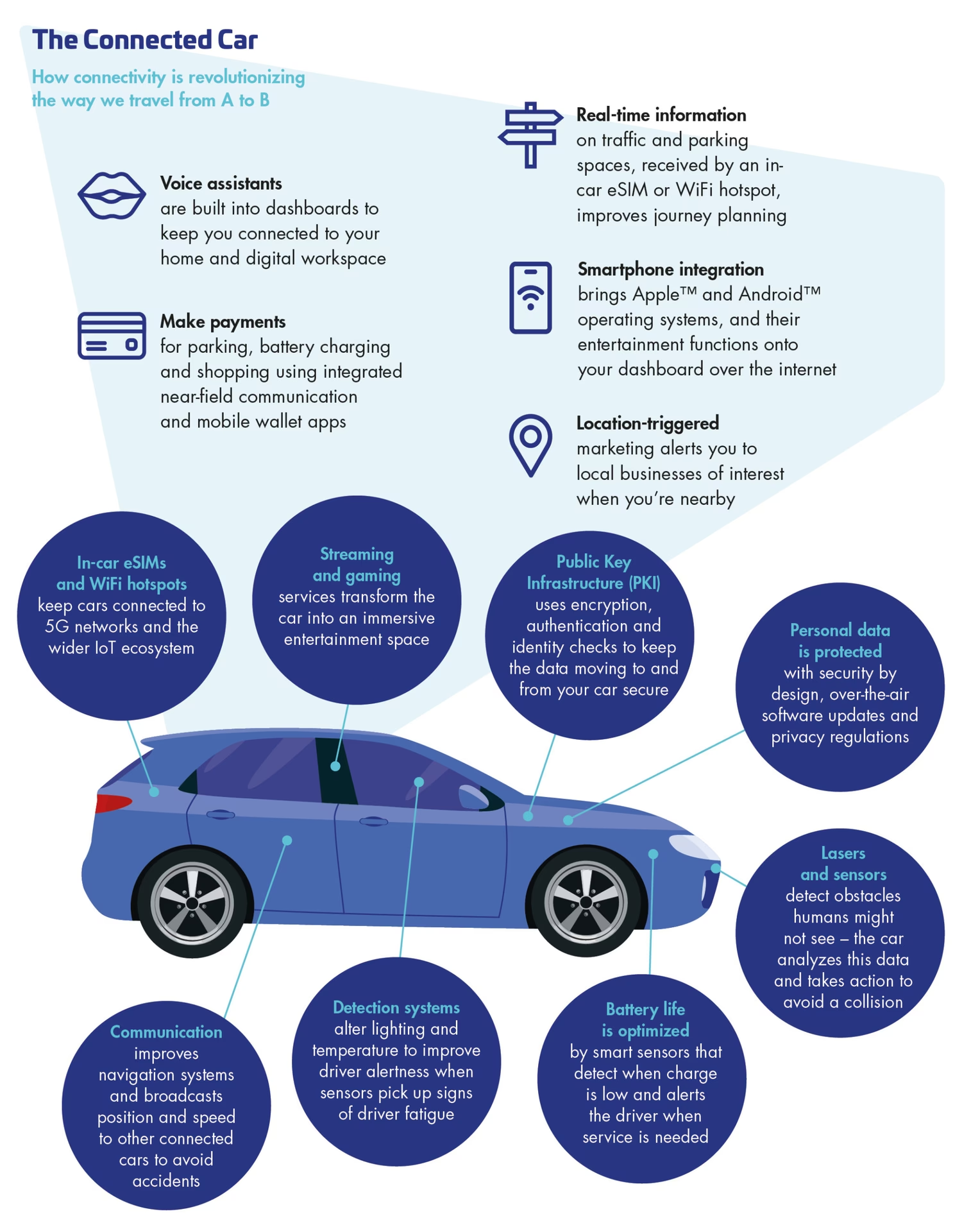
In today's automotive landscape, the 'connected car' is no longer a futuristic concept but a present-day reality. These vehicles, equipped with advanced telematics and internet connectivity, offer a wealth of features, from real-time traffic updates and remote diagnostics to in-car entertainment and over-the-air software updates. However, this increased connectivity also introduces a new frontier for potential threats: cybersecurity. A critical aspect of securing these complex systems is the concept of centralised connected car cybersecurity. This approach aims to provide a robust and efficient framework for protecting the vast amounts of data generated by and transmitted from our vehicles.
The Rise of the Connected Car
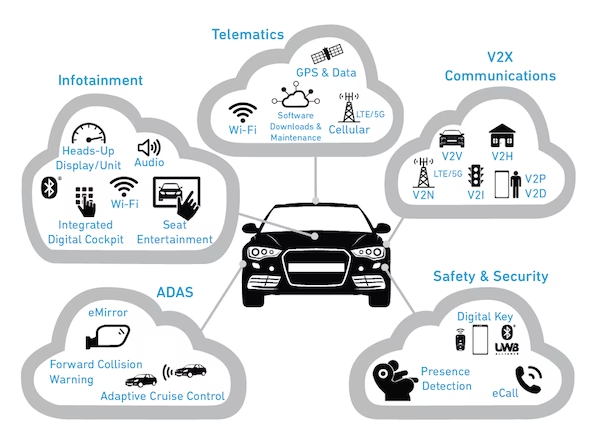
The modern vehicle is essentially a sophisticated computer on wheels. It's a network of interconnected electronic control units (ECUs) that manage everything from engine performance and braking systems to infotainment and advanced driver-assistance systems (ADAS). With the advent of 5G and the Internet of Things (IoT), cars are becoming increasingly integrated into our digital lives. They can communicate with other vehicles (V2V), infrastructure (V2I), pedestrians (V2P), and the network (V2N) – collectively known as V2X communication. This interconnectedness unlocks incredible potential for safety, convenience, and efficiency, but it also exponentially increases the potential attack surface for cyber threats.
What is Centralised Connected Car Cybersecurity?
Centralised connected car cybersecurity refers to a security strategy where the management, monitoring, and mitigation of cyber threats are handled from a single, unified point or platform. Instead of each vehicle operating in isolation with its own independent security measures, a centralised system allows for a more holistic and efficient approach. This central hub can collect data from a fleet of vehicles, analyse it for malicious activity, and deploy security updates or patches across all connected vehicles simultaneously. Think of it as a sophisticated security operations centre (SOC) specifically tailored for automotive networks.
Key Components of a Centralised System
A robust centralised connected car cybersecurity system typically comprises several key components:
- Data Ingestion and Storage: Securely collecting and storing vast amounts of vehicle data at a very low cost is paramount. This includes diagnostic information, sensor readings, communication logs, and user behaviour data. The ability to store large datasets reliably and cost-effectively is crucial for effective analysis.
- Real-time Monitoring and Threat Detection: Continuous monitoring of vehicle networks for anomalies, suspicious patterns, and known attack vectors is essential. This involves using advanced analytics, machine learning, and artificial intelligence to identify potential threats as they emerge.
- Threat Analysis and Intelligence: Analysing detected threats to understand their nature, origin, and potential impact. This also involves gathering threat intelligence from various sources to stay ahead of evolving cyber risks.
- Incident Response and Mitigation: Developing and executing strategies to respond to security incidents, such as isolating a compromised vehicle, patching vulnerabilities, or revoking access.
- Secure Over-the-Air (OTA) Updates: The ability to securely deliver software updates and security patches to vehicles remotely is a cornerstone of centralised cybersecurity. This ensures that vehicles are always running the latest, most secure software.
- Policy Management: Establishing and enforcing security policies across the entire fleet of connected vehicles.
The Benefits of a Centralised Approach
Adopting a centralised model for connected car cybersecurity offers significant advantages:
Cost-Effectiveness and Scalability
Storing and processing the immense volume of data generated by connected vehicles can be prohibitively expensive if not managed efficiently. Centralised systems leverage economies of scale, allowing for the storage of large amounts of vehicle data at a very low cost. This also makes it easier to scale security operations as the number of connected vehicles grows.
Enhanced Security Posture
By aggregating data from an entire fleet, a centralised system can identify broader patterns and emerging threats that might be missed by individual vehicle-based security solutions. This allows for a more proactive and comprehensive defence strategy. The ability to perform transmissions and analyses almost in real-time means that threats can be identified and neutralised much faster, significantly reducing the window of opportunity for attackers.
Improved Incident Response
When a security incident occurs, a centralised system can orchestrate a swift and coordinated response across multiple vehicles. This could involve deploying a patch simultaneously to all affected vehicles, thereby containing the damage and preventing widespread compromise. The rapid dissemination of security fixes is critical in the fast-paced world of cyber threats.
Operational Efficiency
Managing security on a vehicle-by-vehicle basis is inefficient and resource-intensive. A centralised platform streamlines these operations, allowing security teams to focus on higher-level strategic tasks rather than day-to-day management of individual systems.
High Availability and Durability
The infrastructure supporting centralised cybersecurity must be highly available and durable. This means ensuring that the systems are operational and accessible when needed, and that data is protected against loss or corruption. Achieving availability of up to 99.99% and durability of up to 99.999999999% is crucial for maintaining trust and ensuring the continuous operation of connected vehicle services.
Challenges in Implementing Centralised Cybersecurity
Despite its advantages, implementing a centralised connected car cybersecurity system is not without its challenges:
- Data Privacy Concerns: Collecting and analysing vast amounts of vehicle data raises significant privacy concerns. Robust anonymisation techniques and strict data governance policies are essential to protect user privacy.
- Regulatory Compliance: Navigating the complex web of international regulations concerning data storage, privacy, and cybersecurity can be challenging.
- Complexity of Vehicle Architectures: Modern vehicles have incredibly complex and diverse electronic architectures, making it difficult to develop a one-size-fits-all security solution.
- Legacy Systems: Integrating security measures with older vehicle models or existing infrastructure can be a significant hurdle.
- Dependence on Connectivity: The effectiveness of a centralised system relies heavily on consistent and reliable network connectivity for vehicles to communicate with the central platform.
The Future of Connected Car Security
The automotive industry is increasingly recognising the critical importance of cybersecurity. As vehicles become more autonomous and interconnected, the stakes will only get higher. Centralised cybersecurity frameworks are likely to become the standard, evolving to incorporate advanced AI-driven threat detection, blockchain for secure data management, and even more sophisticated methods for ensuring the integrity and safety of connected vehicles. The focus will continue to be on creating a secure ecosystem where drivers can enjoy the benefits of connected mobility without compromising their safety or privacy. The ability to store and retrieve vehicle data at a very low cost will be a foundational element in enabling these advanced security solutions.
Frequently Asked Questions (FAQs)
- What kind of data is collected by connected cars?
- Connected cars can collect a wide range of data, including driving behaviour, GPS location, vehicle diagnostics, infotainment usage, and communication logs. The specific data collected varies by manufacturer and the features enabled.
- How does centralised cybersecurity protect my car?
- A centralised system monitors your vehicle's network for suspicious activity, detects potential threats, and can deploy security updates remotely. This provides a layer of protection against hacking and unauthorised access, similar to how antivirus software works on your computer.
- Is my personal data safe in a connected car?
- Car manufacturers are implementing robust security measures and data privacy policies. However, it's crucial for consumers to be aware of the data being collected and to review the privacy policies of their vehicle's services. Secure data handling is a key aspect of centralised cybersecurity.
- Can a connected car be hacked?
- Yes, like any internet-connected device, connected cars are vulnerable to hacking. This is why strong cybersecurity measures, including centralised systems, are essential to protect against such threats.
- What is V2X communication?
- V2X (Vehicle-to-Everything) communication refers to a vehicle's ability to communicate with other vehicles (V2V), infrastructure (V2I), pedestrians (V2P), and the network (V2N). This technology enhances safety and traffic efficiency but also requires strong cybersecurity protocols.
If you want to read more articles similar to Connected Car Cybersecurity: The Centralised Approach, you can visit the Automotive category.